azure kubernetes服务使用简介
azure账号
申请azure账号,绑定信用卡(目前201906支持visa和万事达的卡 )
创建aks

本地安装azure client工具
linux安装:看这里
windows安装:下载msi文件直接安装
访问aks集群
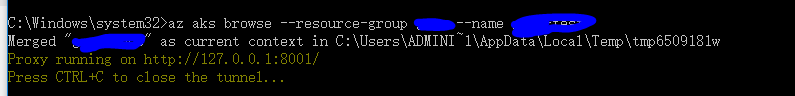
在client中执行以下命令:
az aks get-credentials --resource-group test --name test-test
az aks browse --resource-group test --name test-test
会自动打开浏览器访问http://127.0.0.1:8001,默认控制台会报错:
configmaps is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "configmaps" in API group "" in the namespace "default"
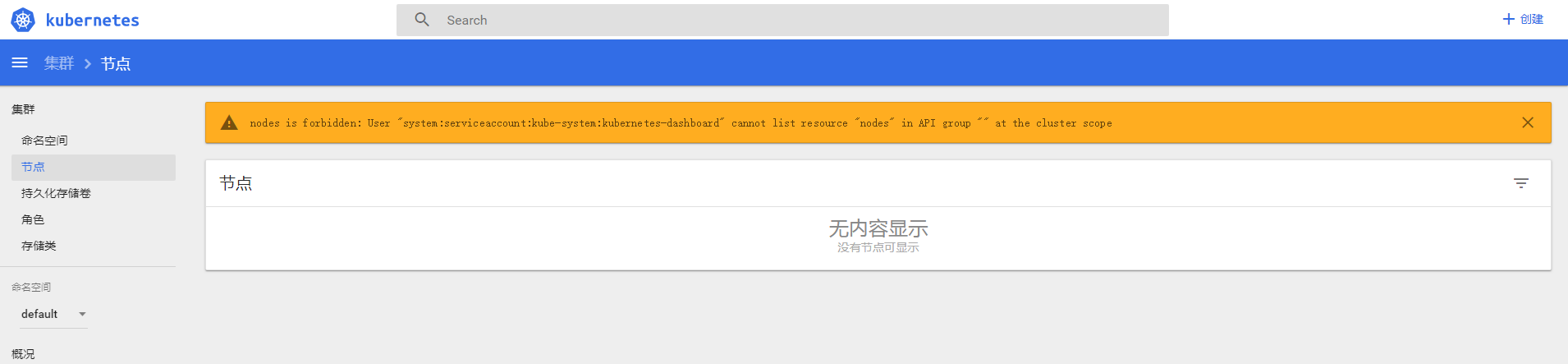
需要增加角色绑定dashboard.yaml,内容如下:
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to create 'kubernetes-dashboard-key-holder' secret.
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
# Allow Dashboard to create 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: kubernetes-dashboard
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
roleRef:
kind: ClusterRole
name: cluster-admin
apiGroup: rbac.authorization.k8s.io
#本地要先安装kubectl二进制
kubectl -f dashboard.yaml
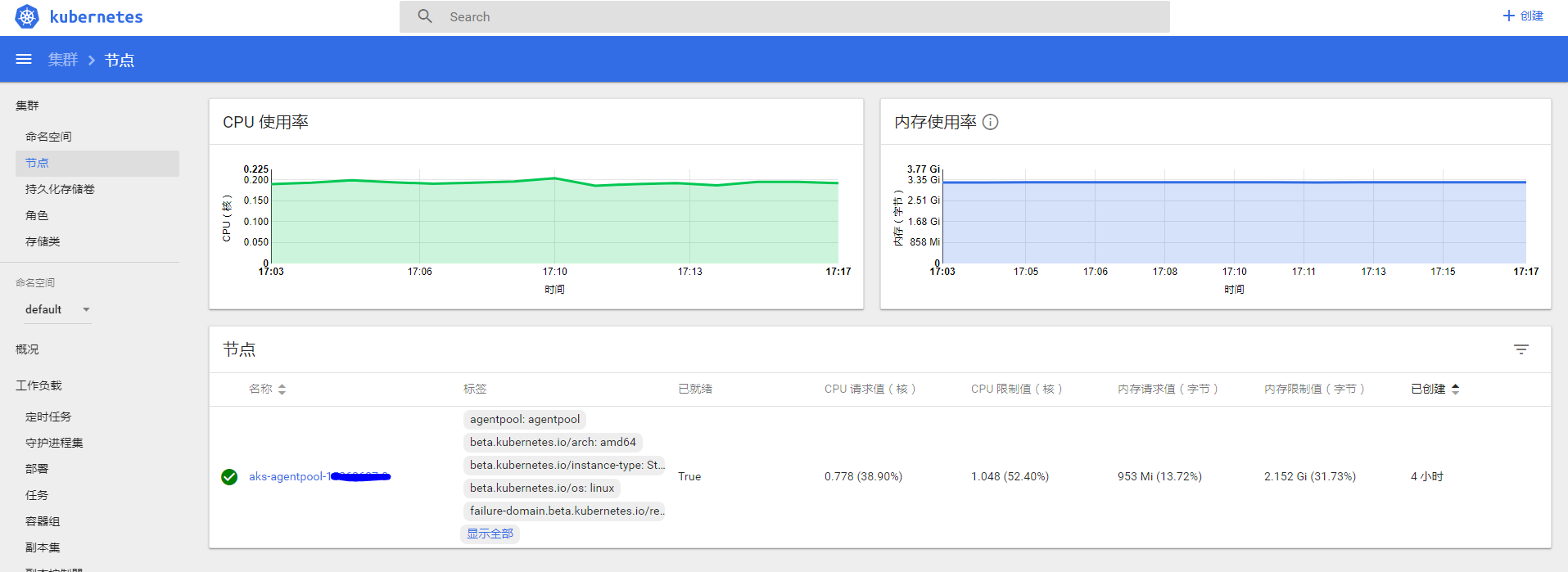
然后访问即可:
namespace
apiVersion: v1
kind: Namespace
metadata:
name: test
deployment
apiVersion: apps/v1
kind: Deployment
metadata:
name: redis
spec:
replicas: 1
selector:
matchLabels:
name: redis
template:
metadata:
labels:
name: redis
spec:
containers:
- name: redis
image: redis
imagePullPolicy: IfNotPresent
ports:
- containerPort: 6379
name: redis
protocol: TCP
service
apiVersion: v1
kind: Service
metadata:
name: redis-internal
annotations:
service.beta.kubernetes.io/azure-load-balancer-internal: "true"
spec:
type: LoadBalancer
#loadBalancerIP: 10.240.0.25
#可以指定静态ip地址
ports:
- port: 6379
- loadBalancerPort: 30000
selector:
name: redis
查看:
[root@db02 ~]# kubectl get service redis-internal -n test
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
redis-internal LoadBalancer 10.0.102.126 10.240.0.35 6379:30236/TCP 104s